
Studio-Grade Security at Every Layer
From encrypted transfers to on-premises AI, Fortify Media is built from the ground up to protect the world's most valuable media content. MovieLabs 2030 compliant. Zero cloud data exposure. Full audit trails.
Compliance and Certifications
Meeting the standards that enterprise content security demands.

SOC 2 Type II
CompliantAnnual SOC 2 Type II audit covering security, availability, and confidentiality. Controls independently verified to meet enterprise procurement trust service criteria.
MPAA Best Practices
AlignedFollows MPAA Content Security Best Practices for secure content handling, physical security, digital security, and asset management. Meets requirements for major studio content security audits.
GDPR
CompliantData processing compliant with GDPR requirements. Data residency controls, right to deletion, and data processing agreements available for European customers.
MovieLabs 2030 Vision
AlignedArchitecture aligned with MovieLabs OMC v2.6.1 principles. Cloud-native, API-first, security-by-design, and designed for the production workflows of the future.
MovieLabs 2030 -- OMC v2.6.1 Implementation
The Motion Picture Laboratories (MovieLabs) 2030 Vision defines the future of production infrastructure. Fortify Media's Fabric product implements the Open Metadata Container (OMC) specification v2.6.1.
Implementation Details:
- 12 OMC entity types fully implemented
- 10 controlled vocabularies for standardized classification
- Automated transformation from ShotGrid entities to OMC-compliant structures
- Vector indexing of all OMC data for high-performance search
- DAM publishing with OMC-normalized metadata
One of the first production platforms to deliver MovieLabs 2030 compliance in an active studio environment.
Encryption at Every Layer
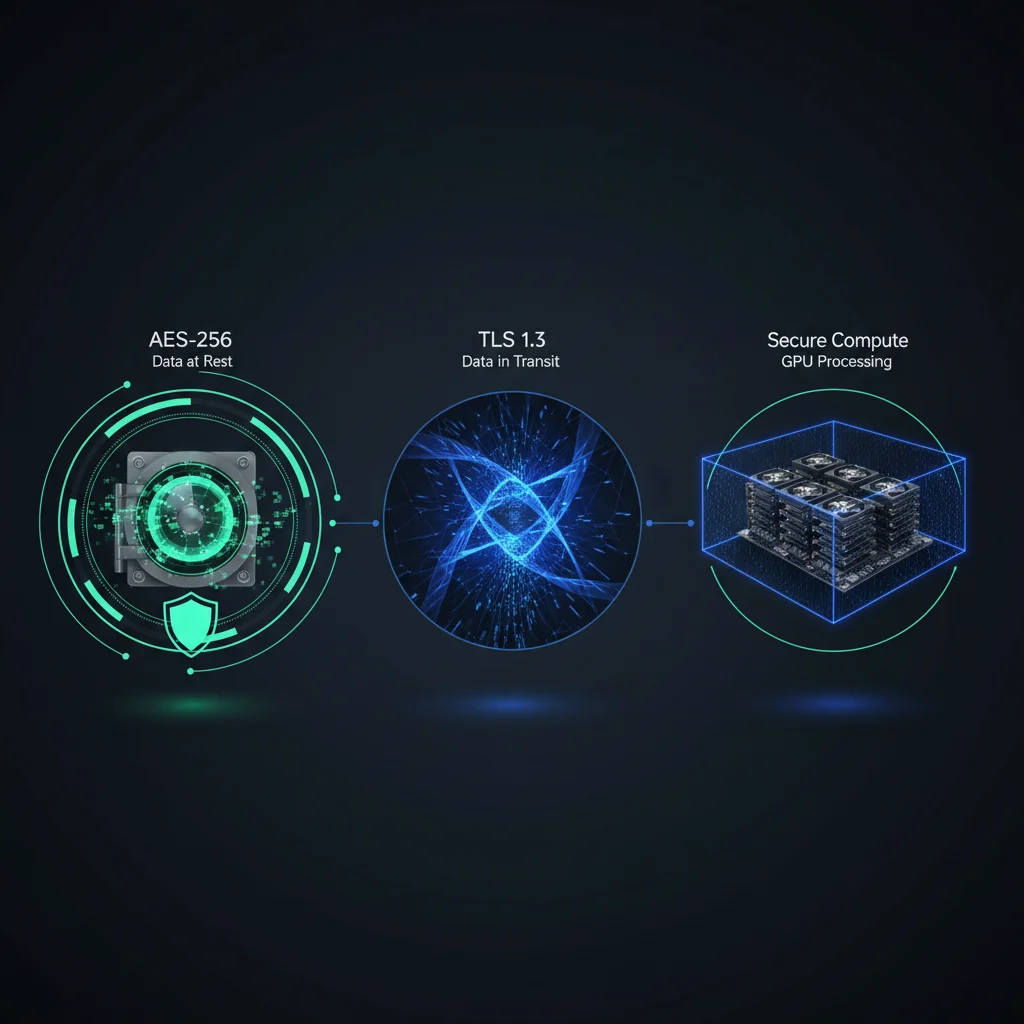
Data at Rest
- AES-256 encryption for all stored media and metadata
- Multi-account AWS with encrypted credential storage (Fernet)
- Separate encryption contexts per production/tenant
Data in Transit
- TLS 1.3+ for all API communications
- IBM Aspera FASP with AES-128 encryption
- HMAC-SHA256 webhook signing
Data Processing
- On-premises AI: E5-large-v2 + Llama 3.1 8B run locally
- No production data sent to external cloud AI services
- GPU processing within your security perimeter
Role-Based Access Control
Granular permissions that match your organizational structure.
Role Hierarchy
Define custom roles with granular permissions. Map roles to your organizational structure -- studio, department, project, user. Admin, Coordinator, User, and Viewer roles with configurable permission sets.
Project-Level Isolation
Each project operates in its own security boundary. Users only see and access the projects they are assigned to. Cross-project access requires explicit grants.
API Key Scoping
API keys scoped to specific projects, products, and operations. Read-only keys, write keys, and admin keys with independent rotation schedules.
Audit Logging
Complete audit trail of every access, modification, and deletion. Tamper-evident logs exportable to your SIEM. Configurable retention policies for compliance.
SSO Integration
SAML 2.0 and OIDC support for single sign-on. Integrate with Okta, Azure AD, Google Workspace, or any compliant identity provider.
IP Allowlisting
Restrict API and UI access to specific IP ranges. Combine with VPN requirements for defense-in-depth network security.
Forensic Watermarking & Leak Tracing

Forensic Watermarking
- Imperceptible markers embedded into video, image, and audio content
- Survives compression, format conversion, cropping, and screen capture
- Unique identifiers per recipient enable leak tracing to exact distribution point
- Applied automatically during processing -- no manual intervention
Visual Watermarking
- Dynamic visible overlays for work-in-progress protection
- Configurable position, opacity, text content, and scaling
- Reusable templates managed through admin interface
- Ideal for department reviews and client approvals
Secure File Transfer at Full Speed
IBM Aspera FASP
- AES-128 encrypted transport protocol
- WAN-optimized: full bandwidth regardless of latency or packet loss
- Resume-capable transfers for reliability
- Fair bandwidth policy to avoid network saturation
Standard Transfers
- SFTP and FTPS for legacy system compatibility
- S3 with server-side encryption and signed URLs
- All transfers logged in audit trail
Regulatory & Privacy Compliance
GDPR Compliance
- Data processing agreements available
- Right to erasure / data deletion capabilities
- Data minimization practices
- EU data residency options
CCPA Compliance
- Consumer data inventory and mapping
- Opt-out mechanisms
- Data disclosure capabilities
- Annual compliance review
Need Detailed Security Documentation?
We provide comprehensive security documentation for enterprise procurement and vendor assessment processes.